Distributed ledger technology operates by connecting multiple participants in a shared environment where information is recorded transparently and securely. This system eliminates the need for a central authority by allowing each member to maintain an identical copy of the data, ensuring trust through collective verification.
At its core, this innovation relies on a consensus mechanism, which enables all parties to agree on the accuracy of transactions or changes without intermediaries. Such agreement protocols prevent fraudulent activities and guarantee that updates are consistent across every participant’s copy.
While the underlying structure might seem complex, the concept is quite simple: imagine a collaborative spreadsheet updated simultaneously by numerous users worldwide. Each entry is time-stamped, linked to previous ones, and validated collectively, forming an unalterable chain of records within this interconnected system.
Understanding the Fundamentals of a Distributed Ledger System
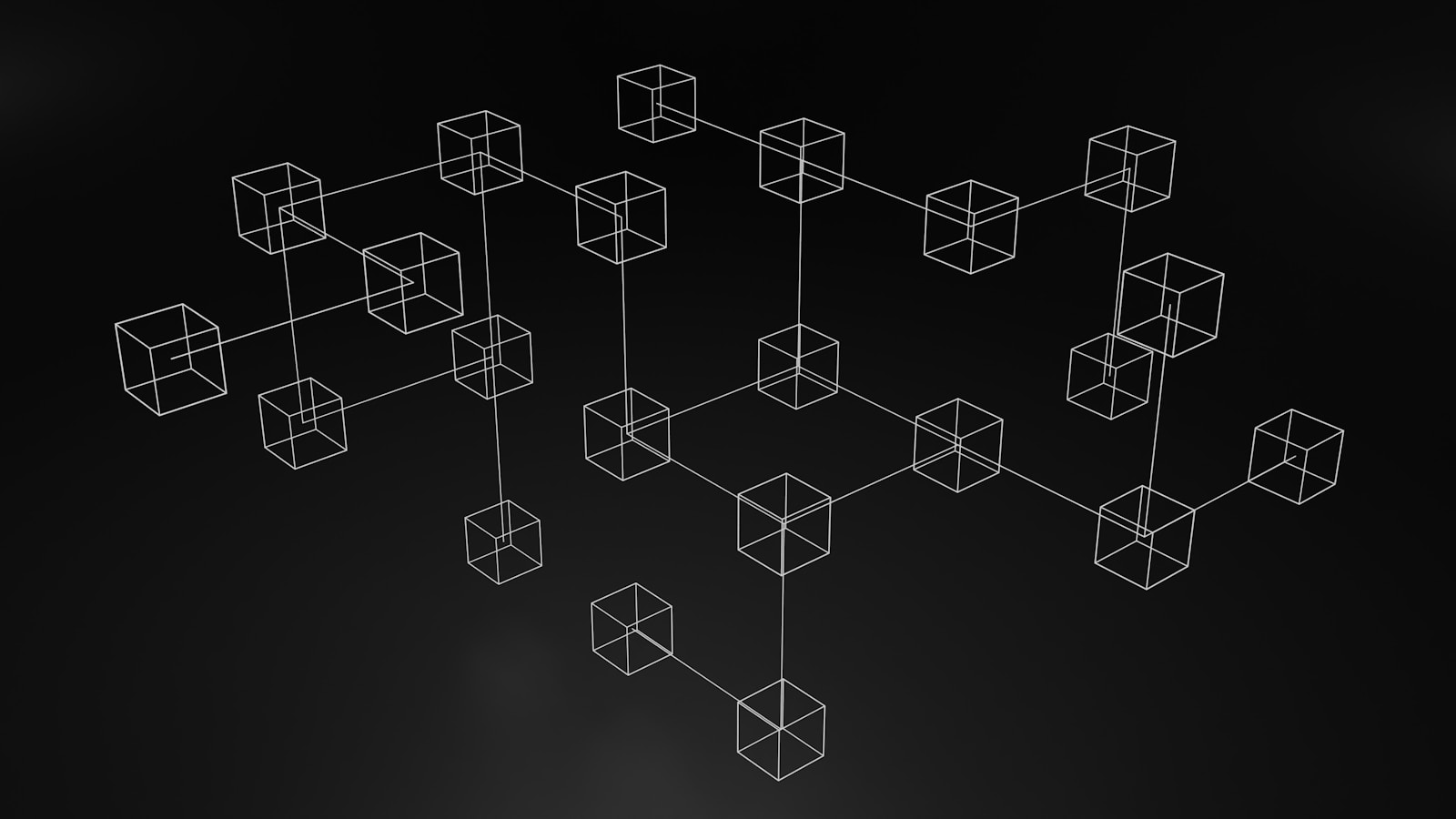
A distributed ledger system operates through interconnected nodes that collectively maintain and verify data records. Each participant in this system holds a copy of the entire ledger, ensuring transparency and resilience against single points of failure. This decentralized approach removes reliance on central authorities by distributing trust across multiple independent entities.
At its core, this technology organizes information into sequentially linked blocks, each containing transaction data verified through cryptographic methods. These blocks form an immutable chain where alteration of past entries requires consensus from the majority of nodes, making tampering computationally impractical.
Key Components and Operational Mechanisms
Nodes serve as individual computers or devices that validate transactions and store copies of the ledger. They communicate continuously to synchronize updates, employing consensus algorithms to agree on valid states. Popular mechanisms like Proof of Work (PoW) or Proof of Stake (PoS) ensure agreement while preventing fraudulent activities.
The consensus process plays a pivotal role by enabling distributed agreement without a centralized arbitrator. For instance, in networks utilizing PoW, miners solve complex mathematical puzzles to propose new blocks; only after verification by other participants are these blocks appended. Such systems balance security with decentralization but may vary in energy consumption and scalability.
The overall infrastructure forms a resilient mesh rather than a hierarchical structure. This design enhances fault tolerance because if some nodes go offline or act maliciously, others continue maintaining accurate records. It also facilitates transparency since every participant can audit transaction histories independently.
Practical applications extend beyond cryptocurrencies into areas such as supply chain management, digital identity verification, and secure voting systems. By leveraging this interconnected framework and consensus-driven validation, organizations achieve higher trustworthiness and traceability compared to traditional databases.
How Nodes Validate Transactions
Transaction validation within a decentralized system hinges on the participation of multiple nodes that collectively verify each operation’s legitimacy. When a transaction is initiated, it is broadcast across the distributed ledger’s participants, where nodes independently check its accuracy based on predefined consensus rules.
Each node functions as a verifier by inspecting transaction details such as digital signatures, account balances, and adherence to protocol constraints. This process ensures that double-spending attempts or fraudulent activities are rejected before being permanently recorded in the ledger.
Step-by-Step Transaction Validation Process
The validation process involves several critical steps performed by nodes:
- Reception and Initial Check: Nodes receive the transaction data and confirm format correctness and signature authenticity using cryptographic algorithms like ECDSA.
- Verification of Inputs: The sender’s balance is checked against the transfer amount to prevent overspending.
- Consensus Compliance: Nodes apply network-specific consensus mechanisms (e.g., Proof of Work, Proof of Stake) to decide if the transaction adheres to system rules.
- Propagation: Validated transactions are shared with other nodes for further confirmation and inclusion in new blocks.
This multi-layered approach guarantees that every participant agrees on the transaction history without relying on a central authority.
The distributed character of this technology means that no single node holds ultimate control; instead, the collective verification power maintains integrity. For instance, Bitcoin nodes validate transactions by checking cryptographic signatures and ensuring inputs have not been previously spent, all while competing miners solve complex puzzles to add validated blocks into the chain.
In contrast, permissioned ledgers like Hyperledger Fabric utilize trusted validating peers that run endorsement policies. These specialized nodes confirm transactions based on organizational rules before committing them to a shared ledger, demonstrating how different systems tailor validation protocols according to their design goals.
Role of Consensus Algorithms
Consensus algorithms are the backbone of any distributed ledger system, ensuring that all participating nodes reach agreement on the state of the shared database without a central authority. By validating transactions and confirming new data entries, these protocols maintain integrity and trust across the decentralized environment. For example, Proof of Work (PoW) employs complex computational challenges to allow nodes to compete for adding blocks, while Proof of Stake (PoS) leverages node ownership in the system as a selection mechanism.
These mechanisms prevent double-spending and resist malicious attempts to alter records by making agreement among nodes mandatory before updates become permanent. The simplicity or complexity of consensus methods directly influences transaction speed, energy consumption, and security levels. Practical systems such as Ripple use the Ripple Protocol Consensus Algorithm (RPCA), which achieves fast confirmation times through unique node lists that simplify agreement processes.
Technical Functions and Examples
Distributed ledgers rely on consensus algorithms to synchronize data across multiple independent participants. The Byzantine Fault Tolerance (BFT) family of algorithms is designed to handle faulty or malicious nodes by requiring a supermajority vote before committing changes. Tendermint is an example implementing BFT in a way that allows near-instantaneous finality ideal for permissioned networks where node identities are known.
Simple consensus models like Practical Byzantine Fault Tolerance (PBFT) operate efficiently within smaller groups but face scalability challenges when applied broadly. On the other hand, Nakamoto Consensus–used in Bitcoin–prioritizes decentralization at scale yet accepts probabilistic finality, meaning confirmations become more trustworthy over time rather than instantly. Each approach reflects trade-offs between throughput, security assumptions, and operational cost that must be carefully balanced depending on network goals.
Benefits of Decentralization
Decentralization fundamentally transforms the way information and authority are managed by distributing control across multiple nodes rather than relying on a single centralized entity. This approach enhances security by eliminating a single point of failure within the system, making it significantly more resistant to cyberattacks and unauthorized tampering. Each node in the distributed architecture holds a copy of the shared ledger, ensuring data redundancy and integrity through continuous cross-verification.
The technology behind decentralized systems employs consensus mechanisms that allow independent participants to agree on transaction validity without requiring trust in one central authority. This process not only increases transparency but also ensures that updates to the system are collectively validated, reducing chances of fraud or manipulation. For example, in permissionless ledgers, consensus algorithms like Proof of Work or Proof of Stake ensure network-wide agreement even when participants are anonymous.
Improved Resilience Through Distribution
A key advantage of decentralization lies in its inherent fault tolerance. Since data is replicated across numerous nodes spread globally, failures or outages affecting some parts do not disrupt overall operation. Consider distributed file storage networks such as IPFS (InterPlanetary File System), which maintain availability despite individual node downtime due to their peer-to-peer structure. This level of robustness is difficult to achieve with conventional centralized databases where a single server malfunction can cause complete service interruption.
Moreover, decentralization helps mitigate censorship risks by removing gatekeepers who could otherwise restrict access or manipulate content. In systems designed for open participation, every node acts autonomously yet cooperatively, enabling users worldwide to engage freely without relying on intermediaries prone to influence from external forces or regulations.
Enhanced Transparency and Trust
The consensus-driven nature of decentralized protocols introduces an auditable environment where transactions are openly recorded and verifiable by all participants. This transparency builds trust among users since each action is traceable and immutable once confirmed by the collective system. For instance, supply chain tracking solutions utilize distributed ledgers to provide stakeholders with real-time insights into product provenance, preventing counterfeit goods infiltration.
This visibility fosters accountability while simplifying compliance with regulatory standards due to easily accessible transaction histories. Unlike opaque traditional databases controlled by single entities, distributed ledgers democratize data ownership and verification responsibilities across many independent operators.
Simplified Network Participation
Decentralized frameworks often lower entry barriers for new participants because they eliminate dependency on centralized authorities for permission or approval. With straightforward setup procedures and open protocols, individuals can join as nodes contributing resources such as computing power or storage space while receiving incentives aligned with their participation level.
This model encourages organic growth and diversity within the system’s ecosystem, demonstrated by cryptocurrency mining pools where miners collaborate without hierarchical control structures yet collectively secure the ledger through coordinated consensus efforts. Such simplicity in joining contributes significantly to maintaining wide distribution essential for sustaining decentralization benefits over time.
Scalability Through Distributed Processing
By distributing workloads among numerous nodes instead of funneling tasks through a central processor, these systems can scale more efficiently under increased demand. Parallel processing enables faster transaction validation speeds as multiple nodes work concurrently while maintaining synchronized states via consensus protocols.
This diversity in protocol design allows tailored solutions optimizing performance according to specific requirements without sacrificing decentralization principles.
Long-Term Sustainability and Innovation
The distributed model promotes continuous evolution driven by community governance rather than top-down mandates. Open-source development combined with collective decision-making empowers contributors worldwide to propose enhancements or fixes transparently evaluated through consensus voting mechanisms embedded within the system’s protocol rules.
This iterative process has led to innovations such as layer-2 scaling techniques that offload transactions from primary chains onto secondary channels while preserving security guarantees provided by underlying networks. As a result, decentralized infrastructures remain adaptable and resilient against emerging challenges while encouraging inclusive participation from diverse stakeholders invested in maintaining system health over time.
Types of blockchain networks
The classification of distributed ledger systems primarily depends on access permissions and the method by which consensus is achieved among participating nodes. Public ledgers are fully open environments where any participant can join, validate transactions, and contribute to data storage. These systems rely heavily on consensus algorithms like Proof of Work (PoW) or Proof of Stake (PoS) to maintain integrity and prevent malicious activity. Ethereum and Bitcoin serve as prime examples, leveraging a decentralized approach that fosters transparency but often faces scalability challenges.
Private ledgers differ significantly, restricting participation to vetted entities within a controlled environment. This permissioned structure enhances transaction speeds and confidentiality while still utilizing cryptographic consensus mechanisms such as Practical Byzantine Fault Tolerance (PBFT). For instance, Hyperledger Fabric is designed for enterprise use cases requiring strict governance over node operation and data visibility. Such systems optimize operational efficiency without sacrificing the core benefits of decentralization.
Hybrid and Consortium Systems
Consortium frameworks combine features from both public and private models by limiting control to a predefined group of organizations while allowing broader read access. This balance facilitates collaboration between multiple stakeholders who share responsibility for maintaining the ledger’s accuracy via consensus protocols tailored for trust among participants. R3 Corda exemplifies this setup in financial sectors, enabling secure yet distributed transaction processing across competing institutions.
The choice of consensus protocol directly influences performance, security, and decentralization levels within these architectures. Distributed nodes communicate continuously to agree on state changes through mechanisms such as Delegated Proof of Stake (DPoS), Federated Consensus, or Byzantine Fault Tolerant algorithms. These techniques ensure resilience against failures or attacks while accommodating different trust assumptions inherent to each system type.
This classification clarifies how various distributed ledger implementations tailor their architecture depending on specific requirements related to trust boundaries, scalability demands, and privacy needs. Understanding these distinctions aids in selecting suitable technologies for particular applications while anticipating potential trade-offs between decentralization and operational control.
Conclusion: Common Use Cases Explained
The distributed ledger technology offers a simple yet powerful solution to trust and transparency challenges across various industries. By leveraging a decentralized system with robust consensus algorithms, it eliminates intermediaries and reduces the risk of single points of failure, enhancing security and efficiency.
Practical applications such as supply chain traceability, cross-border payments, and decentralized identity management illustrate how this architecture transforms existing processes. For instance, in logistics, every transaction is recorded immutably on a shared ledger accessible by all stakeholders, providing real-time visibility and accountability without relying on a centralized authority.
Broader Impact and Future Developments
- Interoperability: Emerging protocols aim to connect multiple distributed systems, enabling seamless data exchange while preserving each’s integrity through consensus mechanisms.
- Scalability: Layer-two solutions and sharding techniques improve transaction throughput without compromising decentralization or security principles.
- Governance Models: Hybrid frameworks combining automated consensus with off-chain decision-making promise more adaptable and inclusive administration of networks.
The continuous refinement of these technologies will expand their accessibility beyond technical experts to everyday users. Understanding the structural role of decentralization and consensus helps demystify why these systems are not just theoretical constructs but practical tools reshaping finance, healthcare, supply chains, and beyond. Encouraging exploration through hands-on experimentation builds confidence in adopting this transformative approach responsibly.